Some days before, Ethical Debuggers presented how Chinese hackers are attacking servers to mine cryptocurrency from them. Today, we are presenting a similar campaign ,which is currently going on ,to mine cryptocurrency from your systems . It was found by Tencent Security Intelligence Team. This time the hackers used a simple phenomenon to attack on your systems. They used a Bluekeep vulnerability which was discovered in early May, an year ago. It was a vulnerability in Microsoft’s Desktop Protocol and allows attacker to execute arbitrary code post exploitation. This vulnerability was regarded as one of the high-risk vulnerability and can be tracked via CVE-2019-0708.
On 6 September 2019, Metasploit launched exploit for the same vulnerability. This vulnerability affects Windows 7, Windows Server 2008 R2, Windows Server 2008, Windows 2003, Windows XP, Windows 8 and Windows 10. Fortunately, later versions are not affected by this vulnerability.
In this campaign the hackers are exploiting this bluekeep vulnerability and inserting a cryptominer Xmring to mine monero cryptocurrency using your system resources. These hackers just used a automated script from github to attack on your systems and then they hijack your system. Is this that foolish? Let’s see the anatomy of the attack.
ANATOMY OF THE ATTACK
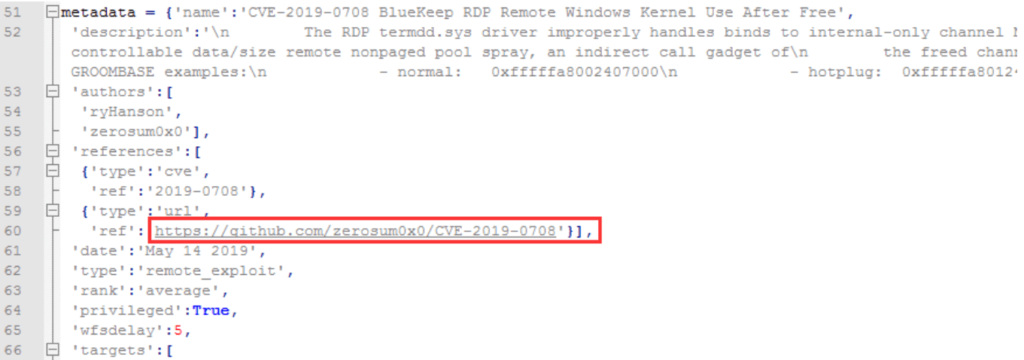
In the first step, the attacker takes the public exploit code of this Bluekeep vulnerability from github https://github.com/zerosum0x0/CVE-2019-0708/
written in python and packs it in .exe file using pyinstaller and finaly generate a scan.exe.
After scan.exe has been finally compiled by the attacker, a randomly scanned range of IP address is being compiled and sent along with it as scan.py. This scan.py is launched with scan.exe into the victim’s system and this files scan vulnerable machines on the victim’s network and finally delivers the malware to that system.
Now the exploit bundle is absolutely ready. Now with some social engineering and phishing techniques, attacker sends this bundle of scan.exe and scan.py to his victims. When victim launches this code into his system, it executes the shell code(exploit code) packed inside the file and creates a Do.vbs( VBsript that is used to compile windows application) in the %Temp% directory of the victim’s system.
Finally after this VBscript file has been created, the main trojan will be downloaded from the domain name hxxp[:]//download.loginserv.net with a name svchost.exe. Officially this svchost.exe is used by windows as Host Processes file, but in this case this file name has been used to confuse the end user that nothing wrong is happening in the background.
This trojan is written in C# and it is obfuscated by simply using a open source tool Dotobfuscator. This code inside .exe file is an assembly which is named as ThanatosCrypter. It checks the system conditions. It check whether the system is in virtual environment or not because in virtual environment , cryptominer is not able to use the physical system resources. A virtual environment is a environment that is created by abstracting hardware from the main computing resources.
This svchost.exe check the following parameter of registry and main windows folder in the running system:
SYSTEM\CurrentControlSet\Enum\SCSI\Disk&Ven_VMware_&Prod_VMware_Virtual_S
SYSTEM\CurrentControlSet\Control\CriticalDeviceDatabase\root#vmwvmcihostdev
SYSTEM\CurrentControlSet\Control\VirtualDeviceDrivers
SOFTWARE\VMWare, Inc.\VMWare Tools
SOFTWARE\Oracle\VirtualBox Guest Additions
C: Drivers\Vmmouse.sys
C:\windows\Sysnative\Drivers\vmci.sys
C:\windows\Sysnative\Drivers\vmusbmouse.sys
C:\windows\Sysnative\VBoxControl.exe
It also checks whether the system is in debugging mode or not. After confirming all the above mentioned states of the system, the svchost.exe finally downloads the main cryptominer from the same domain. The cryptominer being downloaded is the XMRig which is an open source cryptominer to mine Monero cryptocurrency utilizing computing resources. After XMrig has installed into the system, the victim’s machine becomes a cryptominer. Thus, this miner is downloaded from the svchost.exe which is ThanatosCrypter, thus miner is named as ThanatosMiner.
CONCLUSION
The attackers behind this campaigm can only be successful if their system is vulnerable to Bluekeep vulnerability. If the end user’s system is up to date or the user has already installed patched update of windows , this campaign will not affect them. The users must ensure that
- The network to which they are connected is a secure network
- Check their system’s background stats to check the CPU usage, memory usage and run time so that they can see which processes are consuming their computing resources .
- Keep their system up to date with patched version.